Which of the following storage resources provides higher availability and speed for currently used files?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
A cloud solutions architect needs to design a solution that will collect a report and upload it to an object storage service every time a virtual machine is gracefully or non-gracefully
stopped. Which of the following will best satisfy this requirement?
A write-intensive workload is having frequent performance issues. The workload is running on pay-as-you-go VMs. These VMs use SSDs and have appropriate CPU and RAM sizes. The workload writes millions of small files and has a one-year retention requirement. Which of the following actions should be taken?
Department supervisors have requested a report that will help them understand the utilization of cloud resources, make decisions about budgeting for the following year, and reduce
costs. Which of the following are the most important requisite steps to create the report? (Select two).
Which of the following migration types is best to use when migrating a highly available application, which is normally hosted on a local VM cluster, for usage with an external user population?
A company has solid, validated border protection including a next-generation firewall and IPS. However, compromises and breaches continue. Which of the following is the best way to improve the company ' s security controls and reduce the number of incidents?
A company is required to save historical data for seven years. A cloud administrator implements a script that automatically deletes data older than seven years. Which of the following concepts best describes why the historical data is being deleted?
Which of the following is used to deliver code quickly and efficiently across the development, test, and production environments?
A cloud architect is preparing environments to develop a new application that will process sensitive data. The project team consists of one internal developer, two external consultants, and three testers. Which of the following is the most important security control for the cloud architect to consider implementing?
Which of the following are best practices when working with a source control system? (Select two).
A company wants to use a solution that will allow for quick recovery from ransomware attacks, as well as intentional and unintentional attacks on data integrity and availability. Which of the following should the company implement that will minimize administrative overhead?
A company ' s man web application is no longer accessible via the internet. The cloud administrator investigates and discovers the application is accessible locally and only via an IP access. Which of the following was misconfigured?
A company serves customers globally from its website hosted in North America. A cloud engineer recently deployed new instances of the website in the Europe region. Which of the
following is the most likely reason?
A cloud developer resigned from an organization and gave a two-week notice. Within the first week since the developer resigned, a security analyst identifies large volumes of file downloads to the developer’s laptop from the source code repository. Which of the following security controls is the best way to mitigate the organization’s risk of data loss?
A company has been using a CRM application that was developed in-house and is hosted on local servers. Due to internal changes, the company wants to migrate the application to the cloud without having to manage the infrastructure. Which of the following services should the company consider?
A cloud administrator needs to distribute workloads across remote data centers for redundancy reasons. Which of the following deployment strategies would eliminate downtime, accelerate deployment, and remain cost efficient?
A customer is migrating applications to the cloud and wants to grant authorization based on the classification levels of each system. Which of the following should the customer implement to ensure authorisation to systems is granted when the user and system classification properties match? (Select two).
A list of CVEs was identified on a web server. The systems administrator decides to close the ports and disable weak TLS ciphers. Which of the following describes this vulnerability management stage?
Between 11:00 a.m. and 1:00 p.m. on workdays, users report that the sales database is either not accessible, sluggish, or difficult to connect to. A cloud administrator discovers that during the impacted time, all hypervisors are at capacity. However, when 70% of the users are using the same database, those issues are not reported. Which of the following is the most likely cause?
An on-call cloud engineer receives a critical alert about an e-commerce web server being unresponsive. Which of the following steps should the engineer take first?
Given the following command:
Sdocker pull images.comptia.org/user1/myimage:latest
Which of the following correctly identifies images.comptia.org?
A cloud administrator shortens the amount of time a backup runs. An executive in the company requires a guarantee that the backups can be restored with no data loss. Which of th€ following backup features should the administrator lest for?
A technician receives an email from a vendor who is requesting payment of an invoice for human resources services. The email contains a request for bank account numbers. Which of the following types of attacks does this behavior most likely indicate?
Following a ransomware attack, the legal department at a company instructs the IT administrator to store the data from the affected virtual machines for a minimum of one year.
Which of the following is this an example of?
A cloud service provider requires users to migrate to a new type of VM within three months. Which of the following is the best justification for this requirement?
Which of the following best describes a system that keeps all different versions of a software separate from each other while giving access to all of the versions?
A user ' s assigned cloud credentials are locked, and the user is unable to access the project ' s application. The cloud administrator reviews the logs and notices several attempts to log in with the user ' s account were made to a different application after working hours. Which of the following is the best approach for the administrator to troubleshoot this issue?
A developer is sending requests to a SaaS application. The developer becomes unable to send more requests after sending a number of them, but other developers can still send requests. Which of the following is most likely causing the issue?
A cloud administrator deploys new VMs in a cluster and discovers they are getting IP addresses in the range of 169.254.0.0/16. Which of the following is the most likely cause?
A cloud networking engineer is troubleshooting the corporate office ' s network configuration. Employees in the IT and operations departments are unable to resolve IP addresses on all devices, and the IT department cannot establish a connection to other departments ' subnets. The engineer identifies the following configuration currently in place to support the office network:
Each employee needs to connect to the network with a maximum of three hosts. Each subnet must be segregated, but the IT department must have the ability to communicate with all subnets. Which of the following meet the IP addressing and routing requirements? (Select two).
A systems administrator is provisioning VMs according to the following requirements:
· A VM instance needs to be present in at least two data centers.
. During replication, the application hosted on the VM tolerates a maximum latency of one second.
· When a VM is unavailable, failover must be immediate.
Which of the following replication methods will best meet these requirements?
Which of the following compute resources is the most optimal for running a single scripted task on a schedule?
A company is developing a new web application that requires a relational database management system with minimal operational overhead. Which of the following should the company choose?
A company uses containers to implement a web application. The development team completed internal testing of a new feature and is ready to move the feature to the production
environment. Which of the following deployment models would best meet the company ' s needs while minimizing cost and targeting a specific subset of its users?
A cloud engineer needs to migrate an application from on premises to a public cloud. Due to timing constraints, the application cannot be changed prior to migration. Which of the
following migration strategies is best approach for this use case?
A cloud administrator needs to collect process-level, memory-usage tracking for the virtual machines that are part of an autoscaling group. Which of the following is the best way to
accomplish the goal by using cloud-native monitoring services?
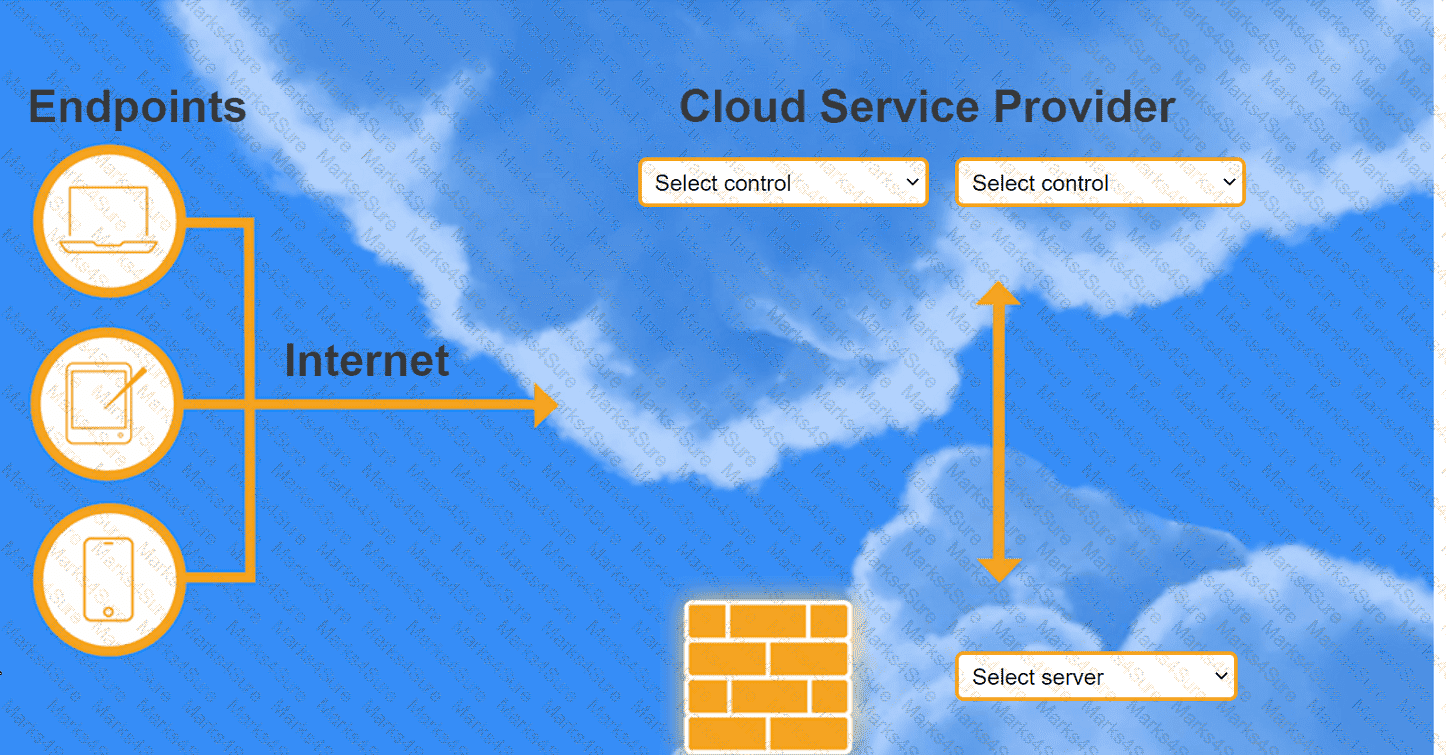
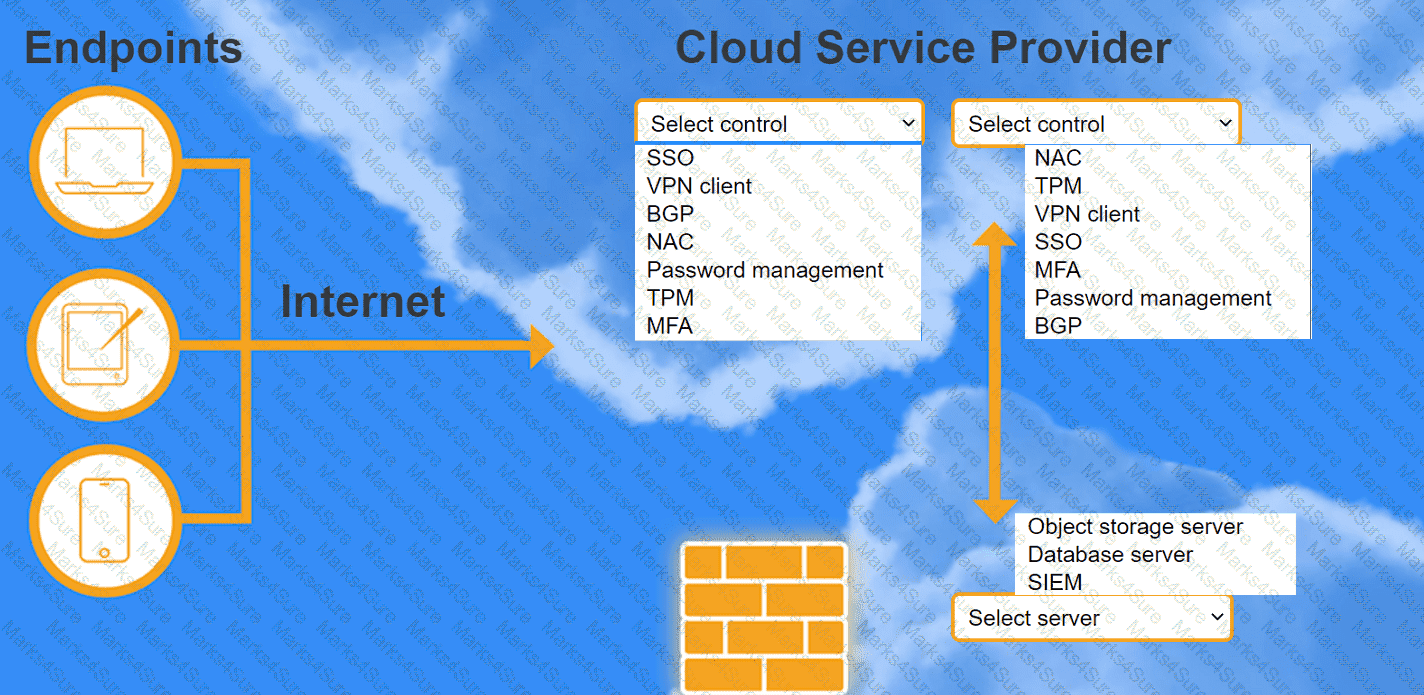
A highly regulated business is required to work remotely, and the risk tolerance is very low. You are tasked with providing an identity solution to the company cloud that includes the following:
secure connectivity that minimizes user login
tracks user activity and monitors for anomalous activity
requires secondary authentication
INSTRUCTIONS
Select controls and servers for the proper control points.
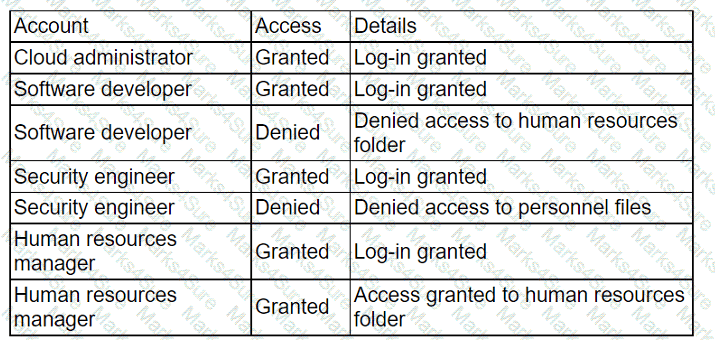
A company migrated its CRM system to a SaaS solution. The security team is updating the RAG matrix for the newly migrated CRM. Given the following table:
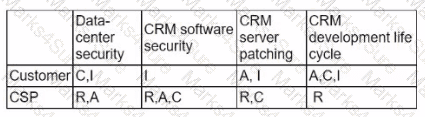
Which of the following responsibility assignments best aligns with the shared responsibility model for the new CRM?
An e-commerce store is preparing for an annual holiday sale. Previously, this sale has increased the number of transactions between two and ten times the normal level of
transactions. A cloud administrator wants to implement a process to scale the web server seamlessly. The goal is to automate changes only when necessary and with minimal cost.
Which of the following scaling approaches should the administrator use?
A cloud engineer needs to integrate a new payment processor with an existing e-commerce website. Which of the following technologies is the best fit for this integration?
A cloud administrator is working on the deployment of an e-commerce website. The administrator evaluates the scaling methods to be implemented when seasonal or flash sales are launched. Which of the following scaling approaches should the administrator use to best manage this scenario?
A cloud engineer is concerned about command-and-control (C2) communication leaving a cloud network over HTTPS. Which of the following should the cloud engineer implement to most efficiently identify this type of communication?
Which of the following is used to detect signals and measure physical properties, such as the temperature of the human body?
An IT security team wants to ensure that the correct parties are informed when a specific user account is signed in. Which of the following would most likely allow an administrator to address this concern?
A company wants to build its new platform using a public cloud. The workload requirements include the following:
• Implementation of custom CIS compliance
• Patch for vulnerabilities within 24 hours
• Warrant at least 1,800 IOPS per volume
Which of the following meets the requirements?
Which of the following technologies should be used by a person who is visually impaired to access data from the cloud?
Which of the following facilitates the continuous deployment of cloud applications without performing a clean install on each iteration?
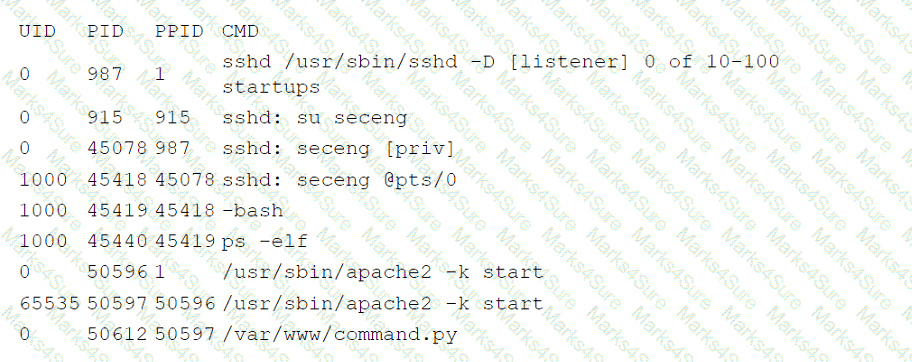
An administrator received a report that company data has been compromised. The compromise occurred on a holiday, and no one in the organization was working. While reviewing
the logs from the holiday, the administrator noted the following details:
The most appropriate action for the cloud security analyst to recommend is using CIS-hardened images. These images are pre-configured by the Center for Internet Security to provide security benchmark standards that help in mitigating vulnerabilities in publicly available container images. References: CompTIA Cloud+ Study Guide (Exam CV0-004) - Chapter on Cloud Security Posture
Which of the following accounts should the administrator disable to prevent a further breach?
Users have been reporting that a remotely hosted application is not accessible following a recent migration. However, the cloud administrator is able to access the application from
the same site as the users. Which of the following should the administrator update?
A developer is building an application that has multiple microservices that need to communicate with each other. The developer currently manually updates the IP address of each service. Which of the following best resolves the communication issue and automates the process?
For compliance purposes, a cloud developer at an insurance company needs to save all customer policies for more than ten years. Which of the following options is the most cost-
efficient tier to save the data in the cloud?
Which of the following will best reduce the cost of running workloads while maintaining the same performance? (Select two).
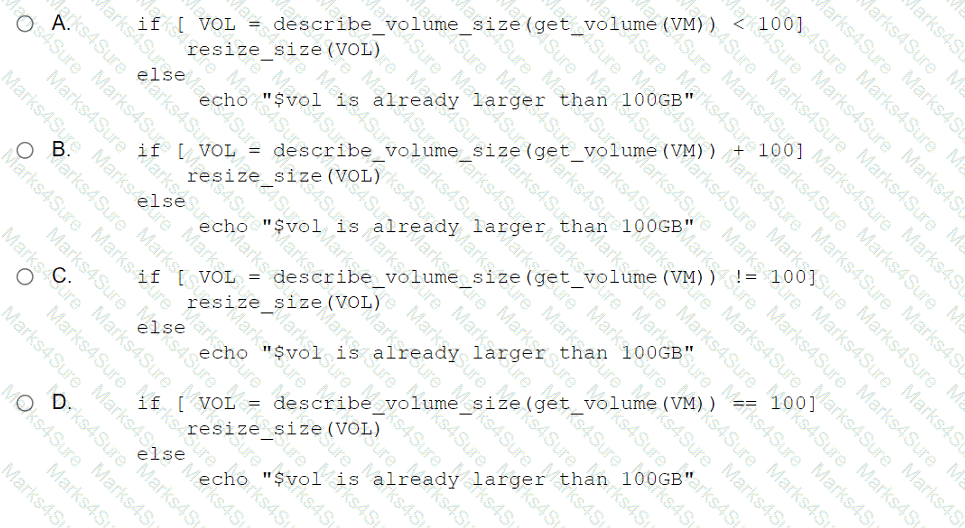
A cloud engineer wants to run a script that increases the volume storage size if it is below 100GB. Which of the following should the engineer run?
A company recently migrated to a public cloud provider. The company ' s computer incident response team needs to configure native cloud services tor detailed logging. Which of the following should the team implement on each cloud service to support root cause analysis of past events? {Select two).
A bank informs an administrator that changes must be made to backups for long-term reporting purposes. Which of the following is the most important change the administrator
should make to satisfy these requirements?
A high-usage cloud resource needs to be monitored in real time on specific events to guarantee its availability. Which of the following actions should be used to meet this requirement?
A cloud engineer is receiving multiple alerts from the infrastructure monitoring agent. The alerts state that all the VMs in the public subnet are at 100% CPU utilization. However, when the engineer checks the network utilization of the VMs, the network throughput is at normal levels. Which of the following is the most likely cause of this issue?
An organization has been using an old version of an Apache Log4j software component in its critical software application. Which of the following should the organization use to
calculate the severity of the risk from using this component?
A cloud deployment uses three different VPCs. The subnets on each VPC need to communicate with the others over private channels. Which of the following will achieve this objective?
The company ' s IDS has reported an anomaly. The cloud engineer remotely accesses the cloud instance, runs a command, and receives the following information:
Which of the following is the most likely root cause of this anomaly?
A company receives files daily from a bank. The company requires that the files must be copied from the cloud storage resource to another cloud storage resource for further
processing. Which of the following methods requires the least amount of effort to achieve the task?
A software engineer at a cybersecurity company wants to access the cloud environment. Per company policy, the cloud environment should not be directly accessible via the internet. Which of the following options best describes how the software engineer can access the cloud resources?
Which of the following provides secure, private communication between cloud environments without provisioning additional hardware or appliances?
A company that has several branches worldwide needs to facilitate full access to a specific cloud resource to a branch in Spain. Other branches will have only read access. Which of
the following is the best way to grant access to the branch in Spain?
A healthcare organization must follow strict compliance requirements to ensure that Pll is not leaked. The cloud administrator needs to ensure the cloud email system can support this requirement Which of the following should the organization enable?
A cloud administrator wants to provision a host with two VMs. The VMs require the following:
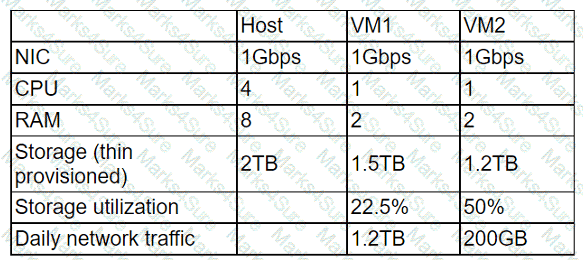
After configuring the servers, the administrator notices that during certain hours of the day, the performance heavily degrades. Which of the following is the best explanation?
Which of the following network protocols is generally used in a NAS environment?
A cloud engineer must update the company’s code repository, which is running on a VM, to the latest version. The engineer downloads and runs the latest update, which appears to be successful. Which of the following steps should the engineer take next?
Which of the transfer when comparing a multiregional to a single-region cloud platform design?
A SaaS provider introduced new software functionality for customers as part of quarterly production enhancements. After an update is implemented, users cannot locate certain transactions from an inbound integration. During the investigation, the application owner finds the following error in the logs:
Error: REST API - Deprecated call is no longer supported in this release.
Which of the following is the best action for the application owner to take to resolve the issue?