Database operation records can be used as ___ evidence to backtrack security events.[fill in the blank]*
An enterprise wants to build a server system and requires the following functions: 1. The enterprise needs to have its own dedicated mailbox, and the sending and receiving of emails needs to go through the enterprise's server; 2. The server must provide file transfer and access services. Users in different departments of the enterprise provide accounts with different permissions: 3. When the enterprise accesses the internal webpage of the enterprise, the enterprise can directly enter the domain name in the browser to access. To meet the above requirements, which of the following servers do enterprises need to deploy? ( )*
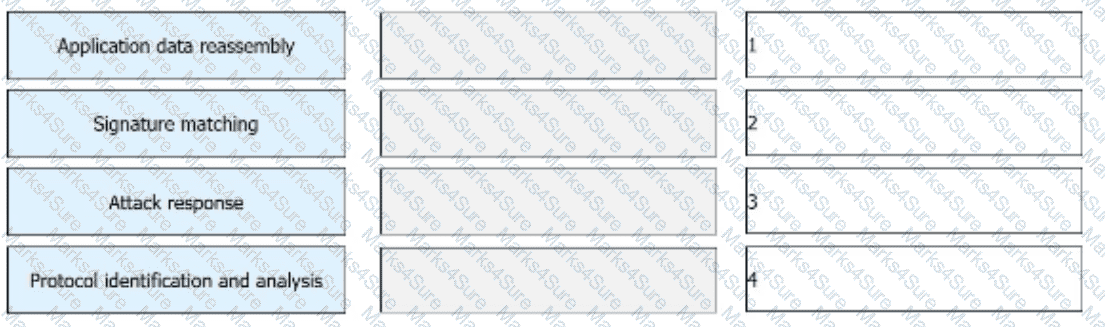
The IPS detects and analyzes all packets passing through a device and determines whether to permit or block the packets in real time based on the comprehensive detection mechanism. Sort the following steps into the correct order based on the basic implementation mechanism of the IPS.
Which of the following attributes are contained in the distinguished name DN in LDAP?
On a firewall, security policies with the permit action do not need to be configured for traffic between users in the same zone.
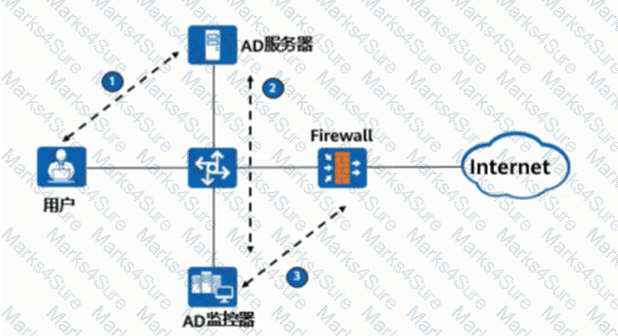
As shown in the figure, the process of AD single sign-on (querying the security log mode of AD server), please match the corresponding operation process.
Huawei Firewall only supports the inter-domain persistent connection function for TCP packets.
Information security aims to protect data in hardware, software, and their systems on information networks to prevent data damage, tampering, or breach due to occasional or malicious reasons and ensure proper system running and non-stop information services.
When the Layer 2 switch receives a unicast frame and the MAC address table entry of the switch is empty, the switch discards the unicast frame.
In the TCP/P protocol core, which of the following protocols works at the application layer?
_____ Authentication is to configure user information (including local user's user name, password and various attributes) on the network access server. The advantage is that it is fast.[fill in the blank]*
Which of the following NAT technologies can implement a public network address to provide source address translation for multiple private network addresses ( )*
3-tuple NAT allows external devices to proactively access internal PCs through translated addresses and ports. Even if no security policy is configured on the firewall, the firewall allows such access packets to pass through.
Which of the following descriptions about the heartbeat interface is wrong ( )?
What is correct in the following description of Security Alliance in IPSec?
There are two ways to set up an IPSec SA
In most cases, a user applies for a local certificate from a CA, and the CA approves the application and issues the certificate to the user.
Which of the following packets is controlled by a firewall's security policy by default?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.
Which of the following statements are correct about the status of the firewall VGMP group?
Sub-interfaces can be created on GE0/0/1 of a firewall. The sub-interfaces can be added to different VLANs, but cannot be added to security zones.
The following description of IDS, which items are correct
The IDS cannot be linked to the firewall.
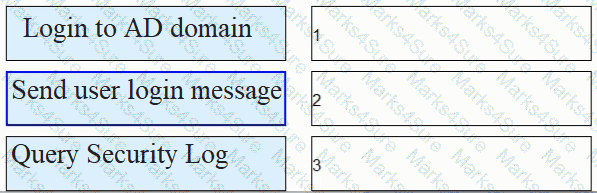
Match the following single-packet attack types with their corresponding descriptions.
What is correct about the following description of device management in the operating system?
Which type of NAT translates both addresses and port numbers and uses the public IP address of the outbound interface as the post-NAT address?
Please order the following steps in the PKI life cycle correctly, 1. Issued, 2. storage, 3. Update, 4. verify[fill in the blank]*
Which of the following statements is correct about security zones on a Huawei firewall?
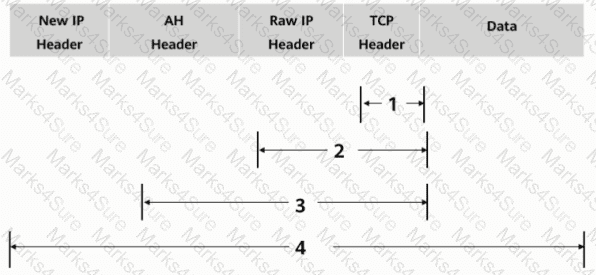
As shown in the figure, what is the authentication range of the AH protocol in tunnel mode?
Which of the following functions help implement IPsec secure transmission of user service data on the Internet by means of encryption and authentication?
When using passive mode to establish an FTP connection, the control channel uses port 20 and the data channel uses port 21.
In the automatic backup mode of hot standby on the second machine, which of the following sessions is backed up?
When logging in to the web UI through HTTPS, you need to specify a local certificate issued by a CA that the web browser trusts for the HTTPS client on the device. Because the web browser can verify the local certificate, this approach avoids malicious attacks and ensures secure logins of administrators.