Network Access Control (NAC) is an end-to-end security control technology that works in combination with AAA to implement access authentication. Which of the following statements about NAC and AAA are true?(Select All that Apply)
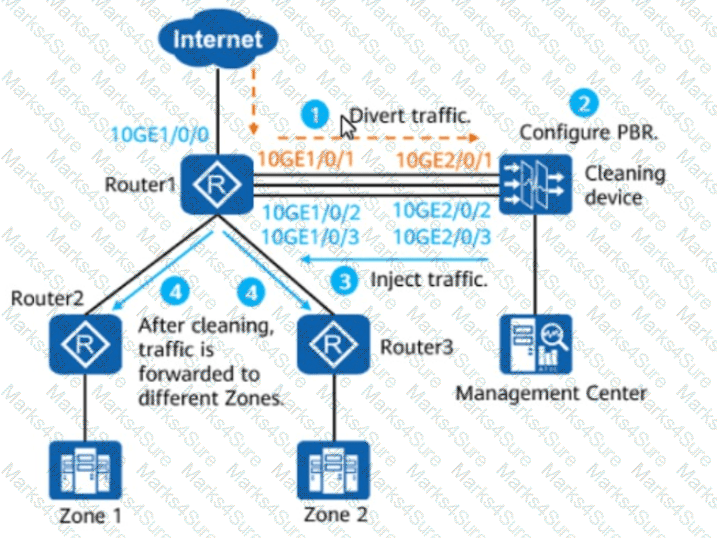
The figure shows the PBR-based injection scenario. Which of the following statements are true about this scenario?(Select All that Apply)
Which of the following methods are used by flood attacks to cause denial of services?(Select All that Apply)
Which of the following technologies does not belong to outbound intelligent uplink selection?
When gateways are connected using GRE over IPsec, the IPsec encapsulation mode must be tunnel mode.
Trojan horses may disclose sensitive information of victims or even remotely manipulate victims' hosts, causing serious harm. Which of the following are the transmission modes of Trojan horses?(Select All that Apply)
HWTACACS is a centralized information exchange protocol based on the client/server structure. It uses UDP for transmission and performs authentication, authorization, and accounting for users accessing the Internet through Point-to-Point Protocol (PPP) or Virtual Private Dial-up Network (VPDN) and administrative users logging in to devices.
Which of the following items are recorded in the IPS service module logs of a Huawei NGFW?(Select All that Apply)
Which of the following is the function of Message 1 and Message 2 during IKEv1 phase-1 negotiation in main mode?
In a Huawei network security environment, which of the following is a key advantage of using HWTACACS over RADIUS for device management authentication?
Options:
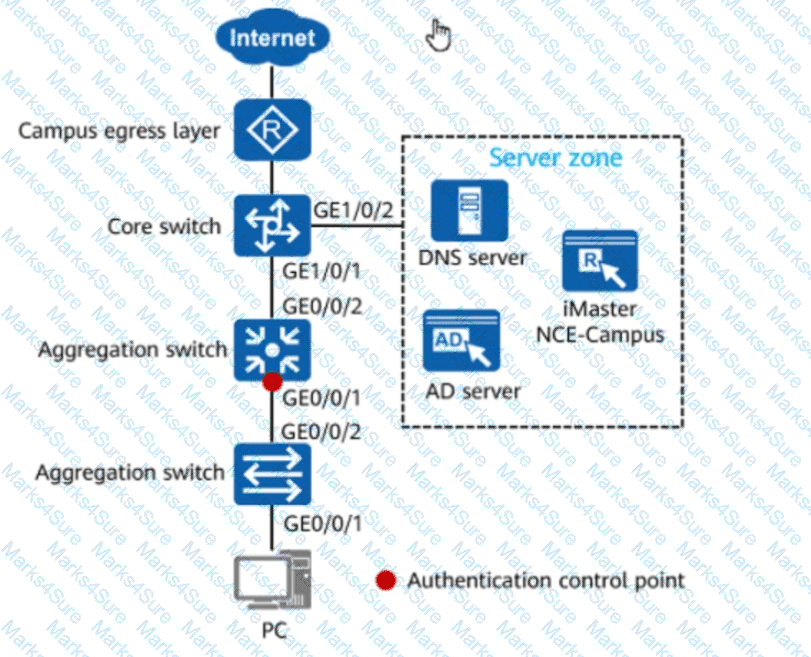
In the figure, if 802.1X authentication is used for wired users on the network, the network admission device and terminals must be connected through a Layer 2 network.
Options:
Which of the following protocols can be encapsulated through GRE over IPsec?(Select All that Apply)
The difference between DoS attacks and DDoS attacks is that DoS attacks are usually directly initiated by attackers, whereas DDoS attacks are usually initiated by attackers controlling multiple zombies.