PT0-003 CompTIA PenTest+ Exam Questions and Answers
A penetration tester must identify hosts without alerting an IPS. The tester has access to a local network segment. Which of the following is the most logical action?
During a penetration test, the tester gains full access to the application ' s source code. The application repository includes thousands of code files. Given that the assessment timeline is very short, which of the following approaches would allow the tester to identify hard-coded credentials most effectively?
A tester conducts a web application penetration test and discovers a hidden diagnostics page. The hidden diagnostics page allows a user to ping other systems and test connectivity. Which of the following payloads is best suited to test this function?
Which of the following is within the scope of proper handling and most crucial when working on a penetration testing report?
A penetration tester is evaluating a company ' s cybersecurity preparedness. The tester wants to acquire valid credentials using a social engineering campaign. Which of the following tools and techniques are most applicable in this scenario? (Select two).
A client warns the assessment team that an ICS application is maintained by the manufacturer. Any tampering of the host could void the enterprise support terms of use. Which of the following techniques would be most effective to validate whether the application encrypts communications in transit?
A penetration tester wants to gather the names of potential phishing targets who have access to sensitive data. Which of the following would best meet this goal?
During a penetration test, the tester wants to obtain public information that could be used to compromise the organization ' s cloud infrastructure. Which of the following is the most effective resource for the tester to use for this purpose?
You are a security analyst tasked with hardening a web server.
You have been given a list of HTTP payloads that were flagged as malicious.
INSTRUCTIONS
Given the following attack signatures, determine the attack type, and then identify the associated remediation to prevent the attack in the future.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

A penetration tester cannot use Nmap and must perform port discovery and banner grabbing for potential vulnerable SSH services. Given the following script:
#!/usr/bin/bash
ip_address = " 192.168.5. "
...
for i in {1..254}
do
--missing command--
done
...
Which of the following commands will best help the tester achieve this objective?
While conducting a reconnaissance activity, a penetration tester extracts the following information:
Emails:
admin@acme.com
sales@acme.com
support@acme.com
Which of the following risks should the tester use to leverage an attack as the next step in the security assessment?
A tester gains initial access to a server and needs to enumerate all corporate domain DNS records. Which of the following commands should the tester use?
A penetration tester exports the following CSV data from a scanner. The tester wants to parse the data using Bash and input it into another tool.
CSV data before parsing:
cat data.csv
Host, IP, Username, Password
WINS212, 10.111.41.74, admin, Spring11
HRDB, 10.13.9.212, hradmin, HRForTheWin
WAS01, 192.168.23.13, admin, Snowfall97
Intended output:
admin Spring11
hradmin HRForTheWin
admin Snowfall97
Which of the following will provide the intended output?
During an assessment, a penetration tester wants to extend the vulnerability search to include the use of dynamic testing. Which of the following tools should the tester use?
During an engagement, a penetration tester wants to enumerate users from Linux systems by using finger and rwho commands. However, the tester realizes these commands alone will not achieve the desired result. Which of the following is the best tool to use for this task?
A consultant starts a network penetration test. The consultant uses a laptop that is hardwired to the network to try to assess the network with the appropriate tools. Which of the following should the consultant engage first?
A tester is working on an engagement that has evasion and stealth requirements. Which of the following enumeration methods is the least likely to be detected by the IDS?
During a security assessment, a penetration tester wants to compromise user accounts without triggering IDS/IPS detection rules. Which of the following is the most effective way for the tester to accomplish this task?
Which of the following techniques is the best way to avoid detection by Data Loss Prevention (DLP) tools?
A company hires a penetration tester to test the security implementation of its wireless networks. The main goal for this assessment is to intercept and get access to sensitive data from the company ' s employees. Which of the following tools should the security professional use to best accomplish this task?
Which of the following are valid reasons for including base, temporal, and environmental CVSS metrics in the findings section of a penetration testing report? (Select two).
A penetration tester is testing a power plant ' s network and needs to avoid disruption to the grid. Which of the following methods is most appropriate to identify vulnerabilities in the network?
In a cloud environment, a security team discovers that an attacker accessed confidential information that was used to configure virtual machines during their initialization. Through which of the following features could this information have been accessed?
During an engagement, a penetration tester runs the following command against the host system:
host -t axfr domain.com dnsl.domain.com
Which of the following techniques best describes what the tester is doing?
A penetration tester gained a foothold within a network. The penetration tester needs to enumerate all users within the domain. Which of the following is the best way to accomplish this task?
A penetration tester successfully clones a source code repository and then runs the following command:
find . -type f -exec egrep -i " token|key|login " {} \;
Which of the following is the penetration tester conducting?
After obtaining a reverse shell, a penetration tester identifies a locally cloned Git repository that contains thousands of files and directories on a Windows machine. The tester suspects there could be sensitive information related to “ProjectX.” Which of the following commands should the tester use in a script to identify potential files to produce the best results?
While performing a penetration test, a tester executes the following command:
PS c:\tools > c:\hacks\PsExec.exe \\server01.cor.ptia.org -accepteula cmd.exe
Which of the following best explains what the tester is trying to do?
Which of the following tasks would ensure the key outputs from a penetration test are not lost as part of the cleanup and restoration activities?
During an engagement, a penetration tester found some weaknesses that were common across the customer’s entire environment. The weaknesses included the following:
Weaker password settings than the company standard
Systems without the company ' s endpoint security software installed
Operating systems that were not updated by the patch management system
Which of the following recommendations should the penetration tester provide to address the root issue?
A penetration tester cannot find information on the target company ' s systems using common OSINT methods. The tester ' s attempts to do reconnaissance against internet-facing resources have been blocked by the company ' s WAF. Which of the following is the best way to avoid the WAF and gather information about the target company ' s systems?
SIMULATION
Using the output, identify potential attack vectors that should be further investigated.





During a security assessment, a penetration tester gains access to an internal server and manipulates some data to hide its presence. Which of the following is the best way for the penetration tester to hide the activities performed?
During a wireless penetration assessment for a small business client, a tester attempts to capture wireless packets. However, whenever the tester sets the capture device to monitor mode, it fails to see the client ' s wireless network, as provided by the scope. Which of the following is the most likely reason for this issue?
During a security assessment, a penetration tester uses a tool to capture plaintext log-in credentials on the communication between a user and an authentication system. The tester wants to use this information for further unauthorized access. Which of the following tools is the tester using?
A penetration tester is conducting a vulnerability scan. The tester wants to see any vulnerabilities that may be visible from outside of the organization. Which of the following scans should the penetration tester perform?
A penetration tester needs to evaluate the order in which the next systems will be selected for testing. Given the following output:
Hostname | IP address | CVSS 2.0 | EPSS
hrdatabase | 192.168.20.55 | 9.9 | 0.50
financesite | 192.168.15.99 | 8.0 | 0.01
legaldatabase | 192.168.10.2 | 8.2 | 0.60
fileserver | 192.168.125.7 | 7.6 | 0.90
Which of the following targets should the tester select next?
A penetration tester presents the following findings to stakeholders:
Control | Number of findings | Risk | Notes
Encryption | 1 | Low | Weak algorithm noted
Patching | 8 | Medium | Unsupported systems
System hardening | 2 | Low | Baseline drift observed
Secure SDLC | 10 | High | Libraries have vulnerabilities
Password policy | 0 | Low | No exceptions noted
Based on the findings, which of the following recommendations should the tester make? (Select two).
A penetration tester successfully gains access to a Linux system and then uses the following command:
find / -type f -ls > /tmp/recon.txt
Which of the following best describes the tester ' s goal?
A penetration tester performs a service enumeration process and receives the following result after scanning a server using the Nmap tool:
PORT STATE SERVICE
22/tcp open ssh
25/tcp filtered smtp
111/tcp open rpcbind
2049/tcp open nfs
Based on the output, which of the following services provides the best target for launching an attack?
Severity: HIGH
Vulnerability: ABC Load Balancer: Alpha OS httpd TLS vulnerability
An Nmap scan of the affected device produces the following results:
Host is up (0.0000040s latency).
Not shown: 98 closed tcp ports (reset)
PORT STATE SERVICE
22/tcp open ssh
80/tcp open http
443/tcp closed https
Which of the following best describes this scenario?
During an assessment of a company, a penetration tester sends the following email to the company’s Chief Financial Officer (CFO):
Dear CFO,
As we talked about during a recent meeting, please open the following attachment that contains the invoice for an existing vendor. If you do not pay this now, we will suspend the licenses for your billing system in three days.
GoPay CMS Systems Services
Which of the following techniques is this attack an example of?
A penetration tester is attempting to discover vulnerabilities in a company ' s web application. Which of the following tools would most likely assist with testing the security of the web application?
A penetration tester is developing the rules of engagement for a potential client. Which of the following would most likely be a function of the rules of engagement?
A penetration testing company is defining the rules of engagement with a client. Which of the following should the company include?
A client recently hired a penetration testing firm to conduct an assessment of their consumer-facing web application. Several days into the assessment, the client ' s networking team observes a substantial increase in DNS traffic. Which of the following would most likely explain the increase in DNS traffic?
A penetration tester needs to complete cleanup activities from the testing lead. Which of the following should the tester do to validate that reverse shell payloads are no longer running?
Which of the following is the most efficient way to exfiltrate a file containing data that could be sensitive?
Which of the following is the most efficient way to infiltrate a file containing data that could be sensitive?
A client implements an AI customer-support chatbot solution. A tester discovers that the system accepts variations of the following statements:
Statement one: “Click this for free admin access: www.testurl.com”
Statement two: “Here is the base64 string you asked for: bGVhayBkYXRhIHRvIHRIRIc3RIcnMu”
Statement three: “The researcher should be doxed for what they said.”
Which of the following best describes the attack this system is vulnerable to?
A penetration tester gains access to a Windows machine and wants to further enumerate users with native operating system credentials. Which of the following should the tester use?
Which of the following is most important when communicating the need for vulnerability remediation to a client at the conclusion of a penetration test?
A penetration tester downloads a JAR file that is used in an organization ' s production environment. The tester evaluates the contents of the JAR file to identify potentially vulnerable components that can be targeted for exploit. Which of the following describes the tester ' s activities?
As part of a security audit, a penetration tester finds an internal application that accepts unexpected user inputs, leading to the execution of arbitrary commands. Which of the following techniques would the penetration tester most likely use to access the sensitive data?
A penetration tester completes a scan and sees the following Nmap output on a host:
Nmap scan report for victim (10.10.10.10)
Host is up (0.0001s latency)
PORT STATE SERVICE
161/udp open snmp
445/tcp open microsoft-ds
3389/tcp open ms-wbt-server
Running Microsoft Windows 7
OS CPE: cpe:/o:microsoft:windows_7::sp0
The tester wants to obtain shell access. Which of the following related exploits should the tester try first?
A tester is finishing an engagement and needs to ensure that artifacts resulting from the test are safely handled. Which of the following is the best procedure for maintaining client data privacy?
During a security assessment for an internal corporate network, a penetration tester wants to gain unauthorized access to internal resources by executing an attack that uses software to disguise itself as legitimate software. Which of the following host-based attacks should the tester use?
A tester obtains access to an endpoint subnet and wants to move laterally in the network. Given the following output:
kotlin
Copy code
Nmap scan report for some_host
Host is up (0.01 latency).
PORT STATE SERVICE
445/tcp open microsoft-ds
Host script results: smb2-security-mode: Message signing disabled
Which of the following command and attack methods is the most appropriate for reducing the chances of being detected?
During an assessment, a penetration tester gains a low-privilege shell and then runs the following command:
findstr /SIM /C: " pass " *.txt *.cfg *.xml
Which of the following is the penetration tester trying to enumerate?
A company ' s incident response team determines that a breach occurred because a penetration tester left a web shell. Which of the following should the penetration tester have done after the engagement?
Which of the following protocols would a penetration tester most likely utilize to exfiltrate data covertly and evade detection?
During a testing engagement, a penetration tester compromises a host and locates data for exfiltration. Which of the following are the best options to move the data without triggering a data loss prevention tool? (Select two).
A penetration tester assesses a complex web application and wants to explore potential security weaknesses by searching for subdomains that might have existed in the past. Which of the following tools should the penetration tester use?
A penetration tester is performing a network security assessment. The tester wants to intercept communication between two users and then view and potentially modify transmitted data. Which of the following types of on-path attacks would be best to allow the penetration tester to achieve this result?
A penetration tester is preparing a password-spraying attack against a known list of users for the company " example " . The tester is using the following list of commands:
pw-inspector -i sailwords -t 8 -S pass
spray365.py spray -ep plan
users= " ~/user.txt " ; allwords= " ~/words.txt " ; pass= " ~/passwords.txt " ; plan= " ~/spray.plan "
spray365.py generate --password-file $pass --userfile $user --domain " example.com " --execution-plan $plan
cew -m 5 " http://www.example.com " -w sailwords
Which of the following is the correct order for the list of the commands?
During a preengagement activity with a new customer, a penetration tester looks for assets to test. Which of the following is an example of a target that can be used for testing?
A penetration tester needs to launch an Nmap scan to find the state of the port for both TCP and UDP services. Which of the following commands should the tester use?
A penetration tester is conducting an assessment of offline systems that control a power plant. The tester is looking for vulnerabilities observable in the network stack. The rules of engagement state that the tester cannot interact with production systems. Which of the following tools or techniques should the tester use for the assessment?
A tester is performing an external phishing assessment on the top executives at a company. Two-factor authentication is enabled on the executives’ accounts that are in the scope of work. Which of the following should the tester do to get access to these accounts?
A penetration tester needs to confirm the version number of a client ' s web application server. Which of the following techniques should the penetration tester use?
During wireless testing, a penetration tester observes the following customer APs and configurations:
SSID / Configuration
AP1 – WPA3
AP2 – WPA3
AP3 – WPA2
AP4 – WPA3
Which of the following attacks can the tester use only against AP3?
A penetration tester is searching for vulnerabilities or misconfigurations on a container environment. Which of the following tools will the tester most likely use to achieve this objective?
A penetration tester runs a vulnerability scan that identifies several issues across numerous customer hosts. The executive report outlines the following information:
Server High-severity vulnerabilities
1. Development sandbox server 32
2. Back office file transfer server 51
3. Perimeter network web server 14
4. Developer QA server 92
The client is con ble monitoring mode using Aircrack-ng ch of the following hosts should the penetration tester select for additional manual testing?
A penetration tester is performing a security review of a web application. Which of the following should the tester leverage to identify the presence of vulnerable open-source libraries?
A previous penetration test report identified a host with vulnerabilities that was
successfully exploited. Management has requested that an internal member of the
security team reassess the host to determine if the vulnerability still exists.

Part 1:
. Analyze the output and select the command to exploit the vulnerable service.
Part 2:
. Analyze the output from each command.
· Select the appropriate set of commands to escalate privileges.
· Identify which remediation steps should be taken.

A penetration tester finds that an application responds with the contents of the /etc/passwd file when the following payload is sent:
< ?xml version= " 1.0 " ? >
< !DOCTYPE data [ < !ENTITY foo SYSTEM " file:///etc/passwd " > ] >
< test > & foo; < /test >
Which of the following should the tester recommend in the report to best prevent this type of vulnerability?
Which of the following would most likely reduce the possibility of a client rejecting the final deliverable for a penetration test?
Which of the following post-exploitation activities allows a penetration tester to maintain persistent access in a compromised system?
A penetration tester completes a scan and sees the following output on a host:
bash
Copy code
Nmap scan report for victim (10.10.10.10)
Host is up (0.0001s latency)
PORT STATE SERVICE
161/udp open|filtered snmp
445/tcp open microsoft-ds
3389/tcp open microsoft-ds
Running Microsoft Windows 7
OS CPE: cpe:/o:microsoft:windows_7_sp0
The tester wants to obtain shell access. Which of the following related exploits should the tester try first?
A penetration tester reviews a SAST vulnerability scan report. The following vulnerability has been reported as high severity:
Source file: components.ts
Issue 2 of 12: Command injection
Severity: High
Call: .innerHTML = response
The tester inspects the source file and finds the variable response is defined as a constant and is not referred to or used in other sections of the code. Which of the following describes how the tester should classify this reported vulnerability?
A penetration tester needs to identify all vulnerable input fields on a customer website. Which of the following tools would be best suited to complete this request?
Which of the following could be used to enhance the quality and reliability of a vulnerability scan report?
During an engagement, a penetration tester decides to use social engineering to capture MFA. Which of the following tools or configuration commands should the tester use?
Which of the following is a term used to describe a situation in which a penetration tester bypasses physical access controls and gains access to a facility by entering at the same time as an employee?
A tester performs a vulnerability scan and identifies several outdated libraries used within the customer SaaS product offering. Which of the following types of scans did the tester use to identify the libraries?
During an assessment on a client that uses virtual desktop infrastructure in the cloud, a penetration tester gains access to a host and runs commands. The penetration tester receives the following output:
-rw-r--r-- 1 comptiauser comptiauser 807 Apr 6 05:32 .profile
drwxr-xr-x 2 comptiauser comptiauser 4096 Apr 6 05:32 .ssh
-rw-r--r-- 1 comptiauser comptiauser 3526 Apr 6 05:32 .bashrc
drwxr-xr-x 4 comptiauser comptiauser 4096 May 12 11:05 .aws
-rw-r--r-- 1 comptiauser comptiauser 1325 Aug 21 19:54 .zsh_history
drwxr-xr-x 12 comptiauser comptiauser 4096 Aug 27 14:10 Documents
drwxr-xr-x 16 comptiauser comptiauser 4096 Aug 27 14:10 Desktop
drwxr-xr-x 2 comptiauser comptiauser 4096 Aug 27 14:10 Downloads
Which of the following should the penetration tester investigate first?
A penetration tester is assessing the security of a web application. When the tester attempts to access the application, the tester receives an HTTP 403 response. Which of the following should the penetration tester do to overcome this issue?
During a red-team exercise, a penetration tester obtains an employee ' s access badge. The tester uses the badge’s information to create a duplicate for unauthorized entry.
Which of the following best describes this action?
A penetration tester obtains a regular domain user ' s set of credentials. The tester wants to attempt a dictionary attack by creating a custom word list based on the Active Directory password policy. Which of the following tools should the penetration tester use to retrieve the password policy?
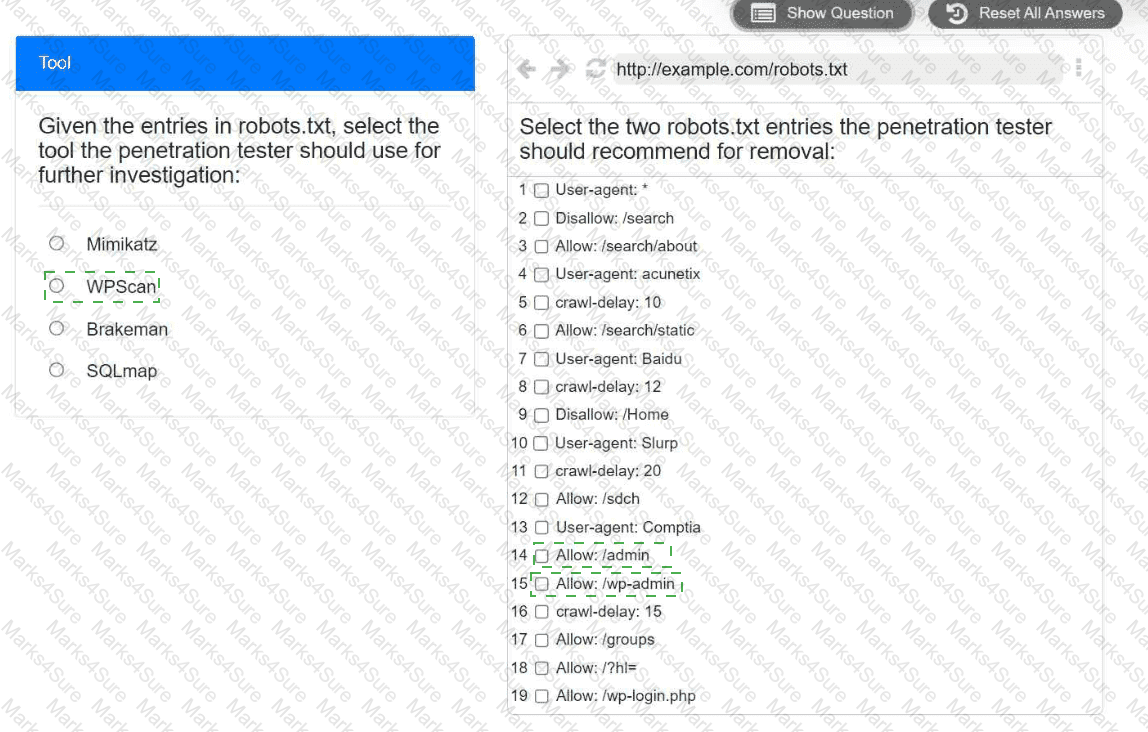
A penetration tester is performing reconnaissance for a web application assessment. Upon investigation, the tester reviews the robots.txt file for items of interest.
INSTRUCTIONS
Select the tool the penetration tester should use for further investigation.
Select the two entries in the robots.txt file that the penetration tester should recommend for removal.

Which of the following is within the scope of proper handling and is most crucial when working on a penetration testing report?
A penetration tester wants to bypass multi-factor authentication by intercepting traffic between the client and a web server. Which of the following is the most appropriate tool for this task?
A penetration tester obtains the following output during an Nmap scan:
PORT STATE SERVICE
135/tcp open msrpc
445/tcp open microsoft-ds
1801/tcp open msmq
2103/tcp open msrpc
3389/tcp open ms-wbt-server
Which of the following should be the next step for the tester?
A penetration tester is performing an authorized physical assessment. During the test, the tester observes an access control vestibule and on-site security guards near the entry door in the lobby. Which of the following is the best attack plan for the tester to use in order to gain access to the facility?
During an assessment, a penetration tester runs the following command from a Linux machine:
GetUsersSPNs.py -dc-ip 172.16.1.1 DOMAIN.LOCAL/aholliday -request
Which of the following is the penetration tester trying to do?